by JB | Oct 14, 2022 | Blog
You constantly search for new tools when trying to streamline business operations. Without the latest technologies, it’s nearly impossible to stay ahead of the competition, scale, or grow your company. Productivity tools make your job easier, allow remote operation,...

by JB | Aug 25, 2022 | Blog
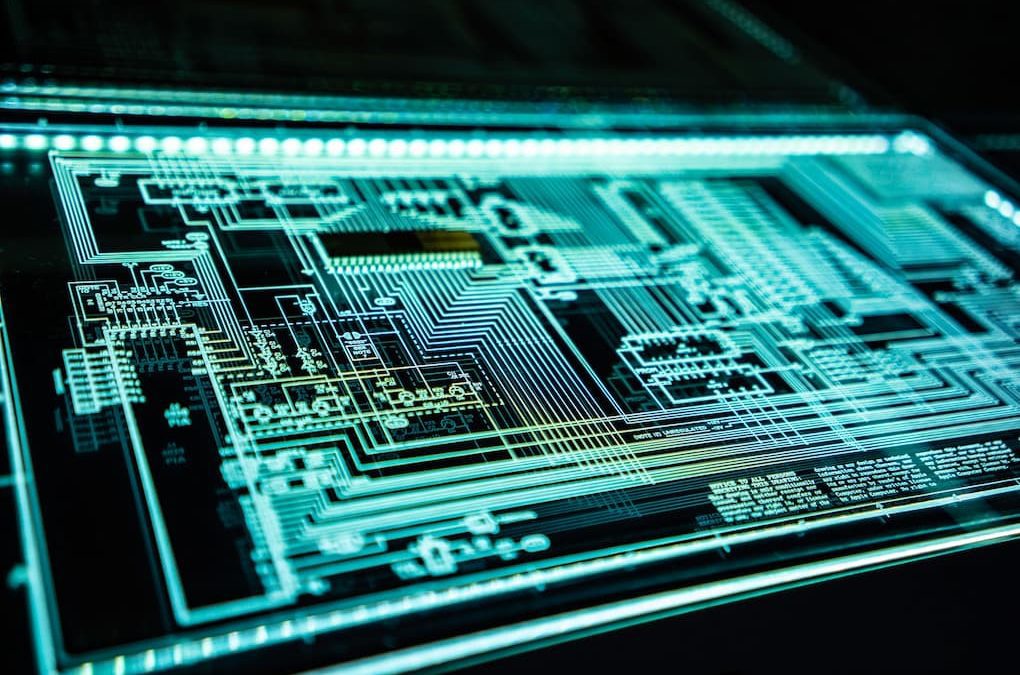
Malware is malicious software that cyber criminals send to your computer or network to collect information, steal money, disrupt your business, and hold your reputation hostage. While malware can wreak havoc on your computer network and valuable data, its effect is...
by JB | Jul 7, 2022 | Blog
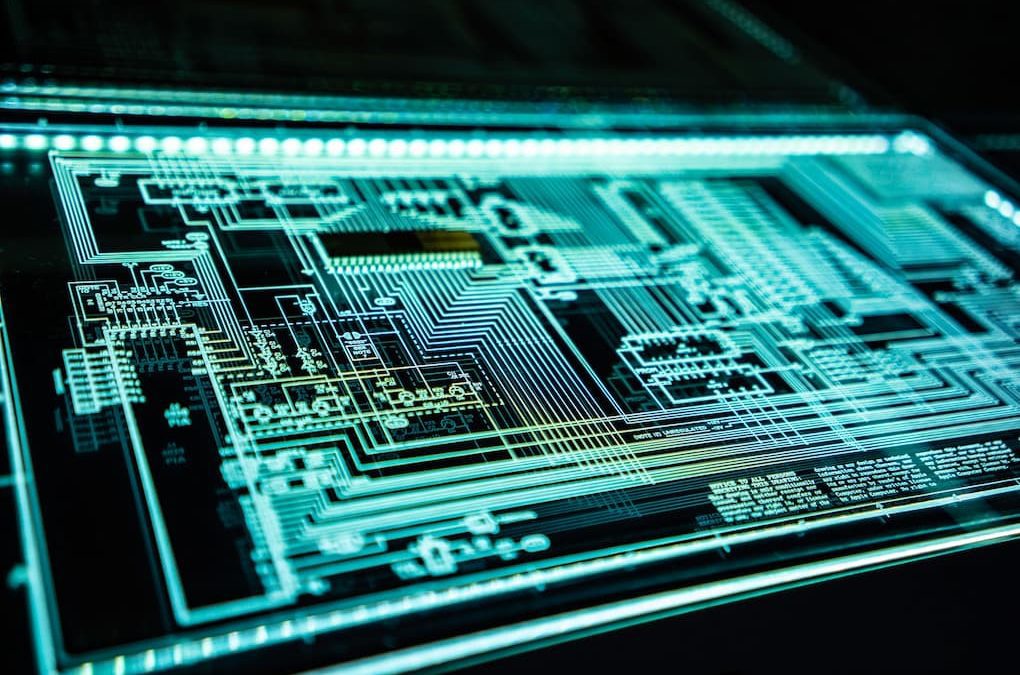
Cybersecurity is a complex set of practices that involves taking the right approach to online operations, internet-facing apps, hardware infrastructure, and data management. The entire system suffers if just one computer inside the network gets exposed. That’s why...

by JB | Jun 16, 2022 | Blog
With cyber-crimes becoming more and more sophisticated, organizations all over the world are arming themselves with strict security measures. From beefing up network security, reviewing password protocols, training employees, and limiting access, the fight for data...

by JB | May 18, 2022 | Blog
As the number of connected devices and computer networks grows, so does the number of cybercrimes. Phishing attacks account for 25% of all cyber breaches, with 85% involving the human element. Most of these attacks could have been prevented simply by training...

by JB | Apr 25, 2022 | Blog
Keeping client data secure is integral to smooth operations and an excellent reputation. Working with sensitive data requires the company to stay compliant with specific rules. If you are processing credit card payments, you’ve probably heard about PCI DSS compliance....